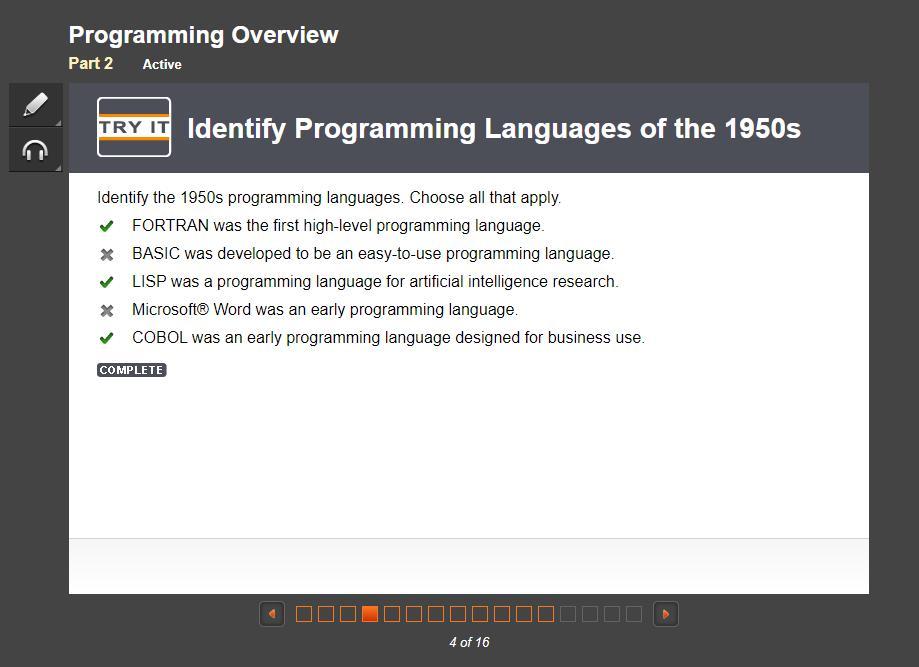
Identify the 1950s programming languages. Choose all that apply.
FORTRAN was the first high-level programming language.
BASIC was developed to be an easy-to-use programming language.
LISP was a programming language for artificial intelligence research.
Microsoft® Word was an early programming language.
COBOL was an early programming language designed for business use.
answer is A, C, E or 1, 3, 5
Answers
The 1950s programming languages are as follows:
A. FORTRAN was the first high-level programming language.
C. LISP was a programming language for artificial intelligence research.
E. COBOL was an early programming language designed for business use.
What is a programming language?A programming language is a special means of communicating with computers to execute certain functions. The advent of computers in the mid-20th century saw the development of languages like FORTRAN, LISP, and COBOL.
Today, there are modern languages that have replaced these ones. Modern languages are more efficient and swifter when compared to their early counterparts.
Learn more about programming languages here:
https://brainly.com/question/16936315
#SPJ1
Answer:
A). FORTRAN was the first high-level programming language.
C). LISP was a programming language for artificial intelligence research.
E). COBOL was an early programming language designed for business use.
Explanation:
I just did the Part 2 on EDGE2022 and it's 200% correct!
Related Questions
what is a method? a procedure that is defined by the developer. a keyword used to loop for a fixed amount of time. a place where we can store data. the type that is given to a variable.
Answers
It is a fundamental concept in object-oriented programming and is used to organize and modularize code.
What is a method?A method is a procedure that is defined by the developer. It is a block of code that performs a specific task and can be called multiple times throughout the program. A method can have input parameters and return a value. It is a fundamental concept in object-oriented programming and is used to organize and modularize code.
It is not a keyword used to loop for a fixed amount of time nor is it a place where we can store data. The type given to a variable is determined by the programmer and can be changed throughout the program as needed.
Learn more about object-oriented programming.
brainly.com/question/26709198
#SPJ11
which deployment of a web server uses network address translation (nat) mapping and is considered the poorest security choice?
Answers
Answer:Reverse Proxy
Explanation:It is the poorest security choice.
during a security audit, you discovered that customer service employees have been sending unencrypted confidential information to their personal email accounts via email. what technology could you employ to detect these occurrences in the future and send an automated alert to the security team? mdm dlp utm ssl see all questions back next question
Answers
Data Loss Prevention (DLP) software
Explanation:
To prevent this from happening in the future and send an automated alert to the security team, you could employ technology such as Data Loss Prevention (DLP) software, which can monitor email activity and detect when confidential information is being sent outside of the organization. Mobile Device Management (MDM) software can also be used to manage and secure employee devices, ensuring that they are not using personal email accounts to send confidential information. Additionally, a Unified Threat Management (UTM) system could be implemented to provide additional security measures such as intrusion detection and prevention, firewall protection, and content filtering. Lastly, implementing Secure Sockets Layer (SSL) encryption for all email communications can also help to prevent unauthorized access to confidential information.
#SPJ11
Security Technology: https://brainly.com/question/31519551
You are a PC technician for a national computer retailer. A business customer asks you to build three custom computers to be used by employees at a branch office. -CAD / CAM design workstation-Home theater PC-Virtualization workstation-2 GB GDDR5 PCIe video adaptor-32 GB PC4-21300 DDR4 RAM-HDMI output
Answers
Build three custom computers for business client: CAD/CAM design, Home theater, Virtualization workstations. Specs: 2GB GDDR5 PCIe video adapter, 32GB PC4-21300 DDR4 RAM, and HDMI output.
As a PC technician for a national computer retailer, I was asked to build three custom computers for a business client. The client requested a CAD/CAM design workstation, a home theater PC, and a virtualization workstation. Each computer was equipped with a 2GB GDDR5 PCIe video adapter, 32GB PC4-21300 DDR4 RAM, and HDMI output. These specifications ensure that each workstation is capable of handling its respective tasks with speed and efficiency. The CAD/CAM workstation can handle complex 3D modeling and rendering, the home theater PC can deliver high-quality audio and video, and the virtualization workstation can run multiple virtual machines simultaneously.
learn more about computer here:
https://brainly.com/question/30146762
#SPJ11
consider the following incident response-related questions. what specifically happened? what was the entry point? what local computers/networks were affected? what remote computers/networks were affected? which task area best describes what i am doing? personnel interviews on scene response initial evaluation incident reporting
Answers
The actions listed in the question relate to the initial stages of an incident response process.
What is the explanation for the above response?The actions listed in the question relate to the initial stages of an incident response process. These stages involve personnel interviews, on-scene response, initial evaluation, and incident reporting.
Personnel interviews are conducted to gather information from individuals who may have witnessed the incident or have knowledge of the affected systems. On-scene response involves deploying resources to contain the incident and prevent further damage. Initial evaluation involves assessing the scope and impact of the incident. Incident reporting involves documenting the incident and providing details to stakeholders.
Therefore, the task area that best describes the actions listed in the question is the initial response stage of incident response.
Learn more about computers/networks at:
https://brainly.com/question/14276789
#SPJ1
• In the initialization phase, test cases are generated to cover two input
variables
• In the horizontal growth phase, the existing test cases are extended
with the values of the other input variables.
• In the vertical growth phase, additional test cases are created such
that the test suite satisfies pairwise coverage for the values of the new variables.
Is a definition of __
Answers
The given text describes a testing methodology which involves three phases: initialization, horizontal growth, and vertical growth. In the initialization phase, test cases are generated to cover two input variables.
Initialization refers to the process of setting initial values for the variables being tested. In the horizontal growth phase, the existing test cases are extended with the values of the other input variables. This is done to ensure that all possible combinations of input values are covered. In the vertical growth phase, additional test cases are created such that the test suite satisfies pairwise coverage for the values of the new variables. Pairwise coverage refers to the testing of all possible pairs of input values. Overall, this testing methodology aims to ensure comprehensive coverage of all input variables and their combinations. The description provided is a definition of a testing strategy known as Combinatorial Test Design (CTD). This strategy involves the initialization phase, horizontal growth phase, and vertical growth phase to systematically generate test cases, extend them with input variables, and ensure pairwise coverage for the values of new variables.
To learn more about methodology click on the link below:
brainly.com/question/30837537
#SPJ11
the network administrator for corpnet.xyz needs to start a powershell remoting session with an on-premises web server named corpweb. what cmdlet do you need to execute? (include the option and parameters necessary to access the specified server.)
Answers
Executing the command, you'll be prompted to enter your password. After successfully authenticating, you'll be in a remote PowerShell session with the CorpWeb server.
To initiate a PowerShell remoting session with the on-premises web server named CorpWeb for the network administrator of CorpNet.xyz, you'll need to use the Enter-PSSession cmdlet with the appropriate options and parameters. Here's the step-by-step explanation:
1. Open a PowerShell console with administrative privileges.
2. To enable PowerShell remoting on the CorpWeb server (if not already enabled), execute the following command:
`Enable-PSRemoting -Force`
3. To start a remote PowerShell session with the CorpWeb server, execute the following cmdlet:
`Enter-PSSession -ComputerName CorpWeb -Credential CorpNet.xyz\YourUsername`
In this command:
- `Enter-PSSession` is the cmdlet used to initiate a remote PowerShell session.
- `-ComputerName CorpWeb` specifies the target server's name.
- `-Credential CorpNet.xyz\YourUsername` specifies the network administrator's domain and username for authentication purposes.
Upon executing the command, you'll be prompted to enter your password. After successfully authenticating, you'll be in a remote PowerShell session with the CorpWeb server.
To Learn More About CorpWeb
https://brainly.com/question/14488599
#SPJ11
tom sees an attacker continually attempt to break into a user account on his linux system from a specific ip address. what can he do to quickly mitigate this issue?
Answers
These will help Tom quickly mitigate the issue by blocking the attacker's IP address, preventing further break-in attempts.
What can he do to quickly mitigate this issue?Tom sees an attacker continually attempt to break into a user account on his Linux system from a specific IP address. What can he do to quickly mitigate this issue?
Identify the attacker's IP address from logs or monitoring tools.
Configure the firewall to block the attacker's IP address. This can be done using the following command in the terminal:
`sudo iptables -A INPUT -s -j DROP`
Replace `` with the actual IP address.
Save the firewall configuration to make it persistent across reboots, using the appropriate command for your Linux distribution.
Monitor the system logs to ensure the attacker's attempts have ceased and verify that the mitigation was effective.
These will help Tom quickly mitigate the issue by blocking the attacker's IP address, preventing further break-in attempts.
Learn more about IP address,
brainly.com/question/31026862
#SPJ11
a user enters a ticket so that the security administrator can grant them access to a file from hr that they need to complete a project. assume all management approvals are in place and the ticket is approved. what kind of access control is this?
Answers
A user submits a ticket so that the security administrator can permit them to access a file from HR that they require to finish a project. Assume the ticket has received permission from management and all necessary authorizations. This DAC is a kind of access control.
What is meant by DAC?Access to objects can be restricted depending on the identity of subjects and/or groups to which they belong using discretionary access control (DAC), a type of access control that is described by the Trusted Computer System Evaluation Criteria (TCSEC). Consider purchasing a DAC (Digital-to-Analog Converter) rather than an amplifier if you're wanting to increase the quality of your audio stream. By lowering noise and distortion, a DAC offers higher sound quality than an amplifier. A DAC is a crucial part of any PC's audio setup. One is present on motherboard audio, as well as on soundcards, smartphones, USB headphones, and other electronic gadgets.To learn more about DAC, refer to:
https://brainly.com/question/30504686
which of the following is not a good reason to network?. question 3 options: a) none. all are good reasons. b) gain access to diverse skill sets c) broaden opportunity d) gain access to private information e) expand power previous page next page
Answers
Reduce the amount of routing table entries by combining several entries is not a strong reason to use a network.
What is network?A group of computers that share resources on or provided by network nodes is referred to as a computer network. To communicate with one another across digital links, computers use standard communication protocols. A set of two or more devices or "nodes" that can communicate together is referred to as a network in computing. It is possible for physical or wireless connections to be made between the involved nodes or devices. The crucial factor is that at least two distinct components are present and are linked. A network is made up of two or more computers connected to share resources (such CDs and printers), transfer files, and enable electronic communication. Cables, phone lines, radio waves, satellites, infrared laser beams, or other technologies can all be used to connect the computers on a network.To learn more about network, refer to:
https://brainly.com/question/1326000
what is the primary difference between fulfillment by amazon (fba) and merchant fulfilled network (mfn)?
Answers
With FBA, Amazon stores, picks, packs, and ships items on behalf of sellers, but with MFN, sellers are responsible for managing every stage of order fulfilment.
Orders on Amazon can be fulfilled in two distinct ways: by Fulfillment by Amazon (FBA) and by Merchant Fulfilled Network (MFN). Sellers that utilise FBA submit their goods to Amazon's warehouses, where Amazon stores, selects, packs, and ships the goods on their behalf. Returns and customer service are also handled by FBA. MFN, on the other hand, mandates that sellers take all responsibility for order fulfillment, including storage, selecting, packing, and shipping. MFN vendors are also in charge of refunds and customer support. The main distinction between the two is that with FBA, Amazon handles order fulfilment and customer support, but with MFN, the seller is in charge of these duties.
Learn more about FBA vs. MFN here.
https://brainly.com/question/31515966
#SPJ11
The primary difference between the term Fulfillment by Amazon (FBA) and the term Merchant Fulfilled Network (MFN) is the party responsible for handling storage, packaging, and shipping of products.
In FBA, Amazon takes care of these tasks. The seller sends their products to Amazon's fulfillment centers, and Amazon stores, packs, and ships the items to customers when an order is placed. Whereas in MFN, the merchant (seller) is responsible for managing inventory, packaging, and shipping the products directly to the customers themselves, without using Amazon's fulfillment services.
Both options have their pros and cons, depending on the seller's specific needs and business goals.
Learn more about Amazon Fulfillment: https://brainly.com/question/28791913
#SPJ11
an example of saas consumer is a company that uses the database servers provided by the cloud service provider to develop software applications. true false
Answers
'The given statement is true because SaaS (Software as a Service) is a cloud computing model where software applications are hosted by a third-party provider and made available to customers over the internet'.
In this model, the provider is responsible for maintaining the servers, databases, and infrastructure required to deliver the software application.A company that uses the database servers provided by a cloud service provider to develop software applications is a great example of a SaaS consumer.
This company can access the database servers and build their applications on top of it without having to worry about managing the underlying infrastructure. They can simply focus on developing their software application while the cloud service provider takes care of the hosting, security, and maintenance of the servers.Using SaaS solutions can provide companies with several benefits including lower costs, greater flexibility, and scalability.
In summary, the statement that an example of a SaaS consumer is a company that uses the database servers provided by the cloud service provider to develop software applications is true. SaaS provides companies with an easy and cost-effective way to access and use software applications without having to manage the underlying infrastructure.
For more such questions on Software as a Service visit:
https://brainly.com/question/14596532
#SPJ11
true or false - to view the cookie information from unencrypted sites, you can implement session hijacking.
Answers
The given statement "To view the cookie information from unencrypted sites, you can implement session hijacking" is true because session hijacking involves intercepting the user's session ID and using it to impersonate the user, thereby gaining access to their cookies.
Cookies can contain sensitive information, such as login credentials or personal information, which can be exploited by an attacker to gain unauthorized access to the user's account or steal their identity.
Session hijacking can be done through various techniques such as sniffing, packet interception, or cross-site scripting (XSS) attacks. It is a serious security threat, and website developers should take steps to prevent it, such as implementing secure session management and using encryption to protect sensitive information.
In summary, session hijacking can be used to view the cookie information from unencrypted sites, making it an effective technique for attackers to gain access to sensitive information. Website developers should take steps to prevent this type of attack and ensure the security of their users' data.
For more questions like Hijacking click the link below:
https://brainly.com/question/29222181
#SPJ11
you are creating a network at home that consists of multiple computers, a high quality printer, and a router with access to a high-speed internet connections. surely you do not need windows server 2008 or oes/netware, but is there a particular desktop operating system that can be installed on each computer that will optimize the operations of your home network?
Answers
There are a few desktop operating systems that can optimize the operations of your home network, depending on your specific needs and preferences. Some popular options include:
Windows 10: Windows 10 includes built-in network features that make it easy to connect and manage devices on your home network. It also includes tools for sharing files and printers, setting up a homegroup, and troubleshooting network issues. macOS: macOS includes similar built-in network features as Windows 10, including the ability to easily connect and manage devices on your network. It also includes tools for sharing files and printers, setting up a home network, and troubleshooting network issues. Linux: Linux is a free and open-source operating system that can be customized to meet your specific needs. It includes powerful network tools and can be used to set up a variety of network configurations, including file sharing, printer sharing, and remote access. Ultimately, the best desktop operating system for your home network will depend on your specific needs and preferences. Consider factors such as ease of use, compatibility with your devices, and the availability of network management tools when making your decision
Learn more about macOS here:
https://brainly.com/question/29763206
#SPJ11
Yes, there are desktop operating systems that can be installed on each computer to optimize the operations of your home network.
1 .Windows 10: This is the latest version of Microsoft's desktop operating system and includes built-in networking features such as HomeGroup for file sharing, network discovery, and network security settings. It also supports a wide range of hardware and software, making it a versatile choice for a home network.
2. macOS: This is Apple's desktop operating system and is designed to work seamlessly with other Apple devices. It includes built-in networking features such as file sharing, screen sharing, and AirDrop for easy file transfer between devices.
3. Linux: There are several distributions of the Linux operating system that can be used for a home network, such as Ubuntu, Fedora, and CentOS. Linux is known for its stability and security, and can be customized to meet specific networking needs.
Whichever operating system you choose, it is important to make sure that it is compatible with your high quality printer and router, and that it is configured properly to take advantage of your high-speed internet connections.
In general, any modern desktop operating system can be used for a home network, as long as it includes basic networking features and supports the hardware and software used in the network. It's also important to ensure that the operating system is kept up-to-date with the latest security patches and updates to protect against cyber threats.
Learn more about operating system:
https://brainly.com/question/30778007
#SPJ11
How long are records of telephone messages retained?A. The same period that the statute of limitations runs for medical professional liability casesB. 5 yearsC. 7 yearsD. 1 week
Answers
The correct answer would depend on the organization or entity in question and thus is a. The same period that the statute of limitations runs for medical professional liability cases
What is the messages about?The length of time that telephone messages are retained can vary depending on the specific context and organization's policies. Therefore, the correct answer would depend on the organization or entity in question.
Therefore, A. The same period that the statute of limitations runs for medical professional liability cases - This option suggests that the retention period for telephone messages would be based on the statute of limitations for medical professional liability cases. However, this would likely not be a standard or common practice for all organizations, as it would be specific to the medical field and related liability concerns.
Read more about telephone here:
https://brainly.com/question/917245
#SPJ1
How long are records of telephone messages retained?
a. The same period that the statute of limitations runs for medical professional liability cases
b. 7 years
c. 1 week
d. 5 years
A. The same period that the statute of limitations runs for medical professional liability cases. This is typically between 2-7 years depending on the state. It is important for healthcare providers to retain these records as they may be needed in the event of a lawsuit or other legal action.
The retention period for telephone messages can vary depending on the context and specific regulations in place. However, considering the options provided
it is most likely that telephone messages are retained for the same period as the statute of limitations runs for medical professional liability cases (Option A). This ensures that any relevant evidence is preserved for potential legal disputes within that time frameThe length of time that records of telephone messages are retained can vary depending on the policies of the organization or business that manages them. However, there are some general guidelines that may apply.In the healthcare industry, for example, the retention period for telephone messages may be determined by state and federal regulations, as well as by the policies of individual organizations. For medical professional liability cases, the statute of limitations varies by state, but it is typically several years. Therefore, in some cases, the retention period for telephone messages may be the same as the statute of limitations for medical professional liability cases.In other industries, the retention period for telephone messages may be determined by business needs or legal requirements. For example, some organizations may choose to retain telephone messages for a certain period of time in case they are needed for legal or regulatory purposes. This retention period may vary, but it is often between 5 and 7 years.In some cases, however, telephone messages may only be retained for a short period of time, such as 1 week. This may be the case for businesses or organizations that receive a high volume of messages and have limited storage capacity or resources for managing them.In summary, the length of time that records of telephone messages are retained can vary depending on the policies of the organization or business that manages them. It may be determined by state and federal regulations, business needs, or legal requirements, and may range from a few days to several years.
To learn more about healthcare click on the link below:
brainly.com/question/12881855
#SPJ11
The Cut command in Windows can be replaced by the keyboard shortcut [Ctrl]+[C]. true or false
Answers
False. The Cut command in Windows can be replaced by the keyboard shortcut [Ctrl]+[X]. The [Ctrl]+[C] shortcut is used for the Copy command.
False.
The Cut command in Windows is typically associated with the keyboard shortcut "Ctrl+X", not "Ctrl+C". "Ctrl+X" is used to cut or move a selected item to the clipboard, while "Ctrl+C" is used to copy a selected item to the clipboard.Using "Ctrl+X" to cut an item is similar to using the Cut command in the right-click context menu or the Home tab in the Ribbon interface in Windows. This command is commonly used to move a file, folder, or text selection to a new location.On the other hand, "Ctrl+C" is used to copy a selected item, which creates a duplicate copy of the item in the clipboard without removing the original item from its original location. This command is commonly used to copy text or files to a new location or to create backups.In summary, while both keyboard shortcuts involve the use of the "Ctrl" key and a letter key, they have different functions, and "Ctrl+X" is typically associated with the Cut command in Windows.
To learn more about shortcut click on the link below:
brainly.com/question/11484367
#SPJ11
a large corporation has modified its network to allow users to access network resources from their personal laptops and smart phones. which networking trend does this describe?
Answers
BYOD is a trend that is here to stay, and companies must adapt their Network infrastructure to accommodate it while maintaining a secure environment.
The networking trend that this scenario describes is Bring Your Own Device (BYOD). This trend has become increasingly popular among businesses and organizations, as it allows employees to use their personal devices, such as laptops, smartphones, and tablets, to access network resources and perform work-related tasks.
BYOD has several advantages, such as increased productivity, as employees can work from anywhere and at any time using their own devices. It also saves the company money, as it eliminates the need for them to provide devices to employees. However, it also poses several challenges, such as security concerns, as personal devices may not have the same level of security as company-provided devices.
To mitigate these challenges, companies must implement policies and procedures to ensure the security of their network and data. This may include requiring employees to install security software on their devices, limiting access to certain network resources, and enforcing strict password policies.
Overall, BYOD is a trend that is here to stay, and companies must adapt their network infrastructure to accommodate it while maintaining a secure environment.
To Learn More About Network
https://brainly.com/question/28342757
#SPJ11
a customer calls the help line to report a computer problem. the help line technician responds and works with the customer for some time. however, the technician cannot identify the root cause of the problem. what should the technician do to help the customer?
Answers
When a help line technician is unable to identify the root cause of a customer's computer problem, there are several steps that can be taken to provide assistance and ensure customer satisfaction.
Firstly, the technician should continue to work with the customer and ask them questions to gain more information about the problem. This can include asking about any recent changes or updates to the computer, any error messages that have appeared, or any specific actions that triggered the issue. By gathering more information, the technician may be able to narrow down potential causes or rule out certain factors.
If this approach still does not lead to a resolution, the technician should consider escalating the issue to a higher level of support. This could involve consulting with a more experienced technician or involving a specialist team that is trained in troubleshooting more complex issues.
Ultimately, the key to helping the customer in this situation is to remain patient, communicative, and proactive. By showing a willingness to work with the customer and explore different options, the technician can help to alleviate their frustration and ensure that they feel supported throughout the process.
For more such questions on computer problem visit:
https://brainly.com/question/30317504
#SPJ11
you can create an object from a concrete class, but not from an abstract class. group of answer choices true false
Answers
This statement is partially true.
In Java, you cannot create an object directly from an abstract class because an abstract class is not fully defined and cannot be instantiated. However, you can create an object from a concrete class that extends the abstract class, and you can use the methods and properties of the abstract class through the concrete class.
For example, suppose you have an abstract class Animal that defines some properties and methods. You cannot create an object directly from this abstract class, as it is not fully defined. However, you can create a concrete class Dog that extends the Animal class, and then create an object of Dog class which can access all the methods and properties of the Animal class.
So, the correct statement would be: "You cannot create an object directly from an abstract class, but you can create an object from a concrete class that extends the abstract class."
Learn more about Animal class here:
https://brainly.com/question/23946982
#SPJ11
The statement "you can create an object from a concrete class, but not from an abstract class." is true.
In computer science, an object is an instance of a class, which is a blueprint or template for creating objects that share common properties and behaviors. An object typically consists of data (also called attributes or properties) and methods (also called functions or procedures) that can operate on that data.
In Java, you can create an object from a concrete class, which is a class that has implemented all of its methods. However, you cannot create an object directly from an abstract class, as it contains at least one abstract method that lacks implementation. Instead, you can only create objects from subclasses that extend the abstract class and provide the necessary implementation for its abstract methods.
To learn more about objects visit : https://brainly.com/question/28732193
#SPJ11
the number of memory-resident processes in contiguous memory allocation systems is typically lower than that of paging-based systems. group of answer choices true false
Answers
In contiguous memory allocation systems, each process is allocated a contiguous block of memory at the time of process creation. This means that the memory space is reserved for the entire process and cannot be shared with other processes. The statement is true.
For such more questions on paging-based systems
https://brainly.com/question/31518798
SPJ11
In contiguous memory allocation systems, each process is allocated a contiguous block of memory at the time of process creation. This means that the memory space is reserved for the entire process and cannot be shared with other processes. The statement is true.
As a result, the total number of memory-resident processes that can be accommodated in the available memory is limited.
Paging-based systems use a virtual memory concept where the memory is divided into smaller fixed-size blocks or pages. Each process is allocated a set of pages, which can be non-contiguous and can be shared with other processes as needed. This allows for more efficient use of memory and enables more processes to be loaded into memory simultaneously.
The number of memory-resident processes in contiguous memory allocation systems is typically lower than that of paging-based systems due to the limitations in allocating contiguous memory blocks for each process.
to learn more about contiguous memory allocation
https://brainly.in/question/2028770
#SPJ11
select the correct statement(s) regarding client-server and peer-to-peer (p2p) networks. a. with client-server networks, you can centralize data storage b. with p2p, the existence of multiple versions of a file is never a problem c. centralizing network security is a strength with p2p network architectures d. client-server networks are considered ad hoc networks
Answers
The correct statement is A) With client-server networks, you can centralize data storage. This is because, in a client-server network, data is stored on a central server which can be accessed by multiple clients.
B) The existence of multiple versions of a file can be a problem in P2P networks. This is because in a P2P network, each peer can have its own version of the file and it can be difficult to ensure that all peers have the same version.
C) Centralizing network security is not a strength of P2P network architectures. This is because in a P2P network, each peer can be a potential security risk, and there is no central authority to enforce security policies.
D) Client-server networks are not considered ad hoc networks. Ad hoc networks are networks that are formed on-the-fly without any pre-existing infrastructure, whereas client-server networks are based on a pre-existing server infrastructure.
Hence the correct statement is A.
You can learn more about client-server networks at: brainly.com/question/30466978
#SPJ11
If all the data fields in a class are private and of primitive types, and the class doesn't contain any setter methods, is the class immutable? True or False?
Answers
True. If all the data fields in a class are declared as private and are of primitive types, and the class doesn't contain any setter methods, then there is no way for any external code to modify the state of the class after it has been instantiated.
Data fields, also known as instance variables or class members, are variables that are associated with an object or a class in object-oriented programming. They represent the state of an object or a class, and can be of different types, such as primitive types, objects, arrays, or other data structures. Data fields are typically declared as private or protected to encapsulate the internal state of an object or a class and prevent external code from accessing or modifying them directly. Instead, accessor methods, such as getters and setters, are used to interact with the data fields, ensuring that they are accessed and modified in a controlled manner. By encapsulating data fields and providing controlled access, object-oriented programming promotes modularity, reusability, and maintainability of code.
Learn more about the data fields here:
https://brainly.com/question/21838436
#SPJ11
if all standard p2pkh locking scripts were replaced by standard p2sh locking scripts for all unspent transaction outputs, what would happen to the size of the utxo set?
Answers
The shift from P2PKH to P2SH locking scripts could result in a smaller UTXO set and more efficient use of space in the blockchain. However, it is important to note that this would require widespread adoption of P2SH by the network, which may not happen overnight.
If all standard P2PKH locking scripts were replaced by standard P2SH locking scripts for all unspent transaction outputs, the size of the UTXO set would likely decrease. This is because P2SH transactions allow for more complex scripts to be hashed into a single address, resulting in a smaller size for each transaction output. With P2PKH transactions, the locking script is longer and more complex, resulting in a larger size for each transaction output.
Additionally, P2SH transactions allow for more flexibility in terms of multi-signature transactions and other complex transaction types. This means that more transactions could be conducted using P2SH, resulting in more efficient use of space in the UTXO set.
To learn more about Blockchain :
https://brainly.com/question/25700270
#SPJ11
Help desk software tools are available for support agents and managers, but few tools are available to help users access a help desk. true or false
Answers
True. Help desk software tools are primarily designed to assist support agents and managers in their tasks, but there are fewer tools available specifically for users to access and navigate help desks. However, some help desk software does include features for user self-service and knowledge management.
False. Help desk software tools are available for both support agents/managers and end-users/customers. While many help desk tools are designed for support agents and managers to track and manage support requests, there are also tools available to help end-users access and submit help desk requests.These tools can take various forms, such as a web-based self-service portal, a mobile app, or an email-based ticketing system. Through these tools, end-users can easily access the help desk and submit support requests, track the status of their requests, and communicate with support agents.In fact, many businesses today recognize the importance of providing a good user experience for their customers and invest in help desk tools that make it easy for customers to access and use their support services. By providing users with efficient and effective support, businesses can enhance customer satisfaction and loyalty, as well as improve their overall reputation and brand image.
To learn more about management. click on the link below:
brainly.com/question/29023210
#SPJ11
what is the main advantage of the microkernel approach to system design? how do user programs and system services interact in a microkernel architecture? what are the disadvantages of using the microkernel approach?
Answers
The main advantage of the microkernel approach to system design is that it provides increased modularity and separation of concernsconcerns.
In this architecture, the microkernel is responsible for the core functionality, while user programs and system services interact through well-defined interfaces.User programs and system services interact in a microkernel architecture via message-passing mechanisms. This enables better isolation, security, and stability, as components communicate without direct access to each other's memory or internal state.The disadvantages of using the microkernel approach include potential performance overhead due to message-passing and the complexity of designing and implementing a well-functioning microkernel-based system.
Learn more about microkernel approach https://brainly.com/question/13384906 here
#SPJ11
The main advantage of the microkernel approach to system design is that it keeps the kernel as small as possible by only including essential functions, such as managing processes and memory, while moving non-essential functions, such as device drivers and file systems, into user-space processes. This results in a more stable and secure system, as any problems with the non-essential functions will not affect the kernel itself.
In a microkernel architecture, user programs and system services interact through inter-process communication (IPC). User programs and system services run as separate processes and communicate with each other through IPC mechanisms, such as message passing or shared memory.
The disadvantages of using the microkernel approach include increased overhead due to the need for IPC, which can lead to decreased performance compared to a monolithic kernel. Additionally, developing and maintaining a microkernel-based system can be more complex and require more resources due to the need for a larger number of processes and the management of IPC mechanisms.
Learn more about microkernel architecture:https://brainly.com/question/14610350
#SPJ11
The Windows operating system simplifies the process of working with documents and apps by organizing the manner in which you interact with the computer.
True or False
Answers
The statement is true.
The Windows operating system provides a graphical user interface (GUI) that simplifies the process of working with documents and apps. Instead of typing commands in a text-based interface, users can interact with the computer using a mouse, touchpad, or touch screen.
The Windows interface features menus, icons, and other visual elements that make it easy to navigate and find what you need. For example, users can open and switch between multiple documents or apps using the taskbar, search for files or programs using the Start menu or Cortana, and manage files and folders using File Explorer. Overall, the Windows operating system is designed to be user-friendly and intuitive, allowing users to focus on their work or tasks rather than on complex technical details.
Learn more about Windows operating system here:
https://brainly.com/question/11496677
#SPJ11
True, the Windows operating system simplifies the process of working with documents and apps by organizing the manner in which you interact with the computer.
This is achieved through features such as the Start menu, taskbar, and file explorer, which provide an intuitive and user-friendly interface for managing tasks, accessing files, and launching applications.
Learn more about the Windows operating system :https://brainly.com/question/31129647
#SPJ11
write a statement that declares an array named streetaddress that contains exactly 80 elements of type char.
Answers
Once the array is declared, individual elements can be accessed using the index notation, for example, streetaddress[0] refers to the first element in the array.
This statement creates an array named "streetaddress" that can hold up to 80 characters. Each element of the array is of type char, which means it can hold a single character such as a letter, number, or symbol. This array can be used to store street addresses or any other information that requires up to 80 characters. Once the array is declared, individual elements can be accessed using the index notation, for example, streetaddress[0] refers to the first element in the array.
Learn more about the array here:
https://brainly.com/question/29849050
#SPJ11
in a binary search tree, all elements below a given a node have values that are > that node's value. group of answer choices true false
Answers
In a binary search tree, all elements below a given node have values that are less than the node's value, not greater than. Therefore, the given statement is false.
What is a binary search tree?A binary search tree (BST) is a data structure that organizes data in a tree-like form. In a BST, each node has at most two child nodes, referred to as the left child and the right child. The left child node contains data that is smaller than the parent node, while the right child node contains data that is greater than the parent node.
The primary advantage of a binary search tree is that it allows for fast searching, insertion, and deletion operations. In a binary search tree, all segments below a given node have values that are less than the node's value. Therefore, the given statement is false.
Learn more about binary search trees, here:
https://brainly.com/question/31605257
#SPJ2
consider a 4-drive, 200 gb per-drive raid array. what is its available storage capacity (in gb) if it is configured as raid-0?
Answers
The available storage capacity of a 4-drive, 200 GB per-drive RAID array configured as RAID-0 is 800 GB.
RAID-0, also known as striping, combines the storage capacity of multiple drives into a single logical volume. In this configuration, data is split across all the drives in the array, which increases the read and write performance of the system but does not provide any redundancy or fault tolerance.
In the case of a 4-drive, 200 GB per-drive RAID-0 array, each drive contributes 200 GB to the overall storage capacity. Because the data is striped across all the drives, the total capacity is the sum of the capacities of each drive, which is 800 GB.
It is important to note that while RAID-0 provides increased performance, it does not provide any data redundancy. This means that if one of the drives in the array fails, all data stored on the array may be lost. Therefore, RAID-0 is typically used in situations where performance is the primary concern and data loss is an acceptable risk.
You can learn more about storage capacity at
https://brainly.com/question/4502035
#SPJ11
a company has multiple cas and intermediate cas issuing digital certificates in different departments, with no one cross-checking their work. which pki trust model should the company use? a. bridge trust model b. web of trust model c. hierarchical trust model d. distributed trust model
Answers
The Hierarchical trust model is the best option for a company with multiple CAs issuing digital certificates in different departments, as it provides centralized control and monitoring of certificate issuance while still allowing for delegation of responsibilities.
The situation presented indicates a lack of coordination and oversight within the company's PKI, which can lead to issues such as duplication of certificates or issuance of fraudulent ones. To address this, the company should implement a PKI trust model that ensures proper control and monitoring of certificate issuance across all departments.Out of the four options presented, the most suitable one for this scenario is the hierarchical trust model. This model involves a central CA that acts as the root of trust for the entire organization, with intermediate CAs that issue certificates to specific departments or areas of the company. This setup allows for better control and coordination of certificate issuance, as the central CA can monitor and audit the work of the intermediate CAs to ensure compliance and accuracy.
The bridge trust model involves two or more independent CAs that agree to trust each other's certificates, but this may not provide enough oversight for the situation at hand. The web of trust model relies on trust relationships between individuals or organizations, which may not be practical for a large, multi-departmental company. The distributed trust model involves multiple CAs that issue and verify certificates, but this may be too complex for the company's needs.In summary, the hierarchical trust model is the best option for a company with multiple CAs issuing digital certificates in different departments, as it provides centralized control and monitoring of certificate issuance while still allowing for delegation of responsibilities.
To Learn More About CAs
https://brainly.com/question/8316419
#SPJ11